Routing an External Registered Apex Domain to an AWS S3 Bucket
Your website will be accessible with HTTP. To access it with HTTPS do these three extra steps:
- Create a certificate with the AWS Certificate Manager for your domain
- Create an AWS CloudFront distribution for your "root" S3 bucket. Associate the certificate to it
- Point the
ALIASrecord of your apex domain to the new CloudFront distribution
How to Point a Naked Domain - Not Registered with Route 53 - to an AWS S3 Hosted Static Website
So people can access your website through example.com instead of www.example.com.
In this post, we're going to connect an apex domain with an AWS S3 hosted website. The naked domain is bought in a domain name registrar other than AWS Route 53. In this case OVH. For other registrars the steps are similar.
Apex domains, generally, cannot
make use of CNAME records. Allowed are A or AAAA records, pointing to
static IPs. This makes it harder to use our naked domain for
our website: example.com. This is because of the dynamic nature of AWS S3 instances. They expose a
subdomain endpoint, so they can route the internal traffic with freedom.
Let's start.
Copy your current zone file
Log in to your OVH account, go to: Domains > DNS zone, and reduce the TTL (Time to Live).
The authoritative name servers cache will expire faster now. This is good because we're going to change the NS (Name Server) records.
Now click on: DNS zone > Change in text format, and copy your RRs (Resource Records).
It should look like:
$TTL 3600
@ IN SOA dns18.ovh.net. tech.ovh.net. (2019112215 86400 3600 3600000 300)
IN NS dns18.ovh.net.
IN NS ns18.ovh.net.
IN MX 100 mx3.mail.ovh.net.
IN MX 1 mx1.mail.ovh.net.
IN MX 5 mx2.mail.ovh.net.
IN A ???
IN AAAA ???
IN TXT "1|www.rubenbelow.com"
600 IN TXT "v=spf1 include:mx.ovh.com ~all"
_autodiscover._tcp IN SRV 0 0 443 mailconfig.ovh.net.
_imaps._tcp IN SRV 0 0 993 ssl0.ovh.net.
_submission._tcp IN SRV 0 0 465 ssl0.ovh.net.
autoconfig IN CNAME mailconfig.ovh.net.
autodiscover IN CNAME mailconfig.ovh.net.
ftp IN CNAME rubenbelow.com.
imap IN CNAME ssl0.ovh.net.
mail IN CNAME ssl0.ovh.net.
pop3 IN CNAME ssl0.ovh.net.
smtp IN CNAME ssl0.ovh.net.
www IN CNAME ???Some values are replaced with: ???
In the next step, we're going to import our entries in AWS Route 53. Before, let us delete some entries.
Records to delete:
IN NS dns18.ovh.net.
IN NS ns18.ovh.net.
...
IN A ???
IN AAAA ???
...
www IN CNAME ???Create an AWS Route 53 Hosted Zone
Log in to your AWS console, go to Route 53,
and click on: Create Hosted Zone. As: Domain Name, use the name of your apex domain: example.com.
Modify your DNS file SOA record
Before starting with the next step we need to change the SOA (Start of Authority) record to match
the new one.
Change:
@ IN SOA dns18.ovh.net. tech.ovh.net. (2019112215 86400 3600 3600000 300)To the SOA record in your new Hosted Zone.
The entry should now be like:
@ IN SOA ns-289.awsdns-36.com. awsdns-hostmaster.amazon.com. 1 7200 900 1209600 86400Import your DNS file into Route 53
Now that we have a fresh hosted zone we'll import the RR records we exported from OVH.
Do not import the previously deleted NS, A, and AAAA records!
- Click on your new Hosted Zone:
example.com(you'll see a list of RRs) - Click on: Import Zone File
- Paste your previously exported
DNSrecords - Import your
DNSrecords
If you get: "Error parsing zone file: One resource cannot have multiple distinct TTL values". Delete the mismatching
TTL from the zone file.
From:
600 IN TXT "v=spf1 include:mx.ovh.com ~all"To:
IN TXT "v=spf1 include:mx.ovh.com ~all"Add an ALIAS record
So far, so good.
Now we add an A ALIAS record for the naked domain; example.com pointing to our AWS S3 bucket.
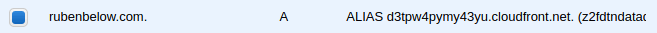
It should be like this but with an S3 bucket URL instead of a CloudFront URL
Do the same now with an AAAA record.
Add a CNAME record
Add a CNAME record for your www subdomain pointing to your apex domain: example.com.
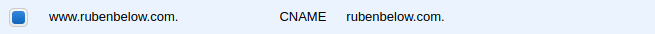
It should be like this
Get your new NS entries
Get the values of your NS entry. We're going to use them at OVH in the next step.
They should be like:
ns-289.awsdns-36.com.
ns-1715.awsdns-22.co.uk.
ns-1241.awsdns-27.org.
ns-740.awsdns-28.net.Add your new AWS NS values to your domains registrar
In your OVH account go to: DNS servers
- Delete the old OVH
NSrecords - Add your new AWS
NSrecords
Good to go.
Troubleshooting
The changes will take some time to propagate (sometimes up to 24h). We can check the state of the DNS (Domain Name Server) update on:
If the DNS update is done but you cannot access example.com through your computer, it could be that your ISP (Internet Service Provider) still
did not update their RR cache. In this case, you should be able to access your website through a VPN.
Thanks for learning with this tutorial.
Follow me on GitHub.
If for some casual the indications did not work for you; don't mind to drop me a line with the infringing points. I'll update the post correspondingly.